The article is concerned with the issue of cybersecurity in Latin America region. The paper takes into consideration the prerequisites that fostered the rampant growth of informational potential in Latin America, as well as the vulnerabilities of the regional nations in the realm of their informational security. In addition, the article draws attention to the most-developed states’ experience in this spheres, and its possible application in Latin America.
Keywords: Latin America, cybersecurity, international relations.
We live in an era of high-informational technologies and sophisticated informational networks. Through the Internet, we check our mail, make orders in online shops, share personal and private information with our colleagues and mates. On the other hand, these advantages of modern, information-addicted lifestyle made us tremendously vulnerable to the threats of informational crimes. Now it is not necessary to hire a killer to make pressure in a person, you just can ask the help of a professional hacker who can find private or compromising date; thus you obtain leverages of influence on your victim. More than that, nowadays informational enforcement is one of the mechanisms most frequently used by national governments to influence citizens who do not agree with the main line policy within the state or have some alternative views which contravene the government's course.
This problem is crucially important in the context of Latin America, where over half the population uses the Internet and the rate of the usage is one of the highest in the world. Nevertheless, the majority of countries in the region do not have cybersecurity strategies therefore the same technology that enables entities to communicate, collaborate, trade and conduct business in real time also creates the risk of malicious actors gaining access to information. Motivations range from monetary gain to intellectual property theft, and even data destruction [1]. In the long term, cyberinsecurity may have a negative influence on economic and social development of the countries. That is why, combating cybercrime and strengthening cyberresilience should be considered critical cornerstones of domestic and foreign policy.
The global cybercrime industry is significantly bigger that most of the major and well-known industries, such as the illegal drugs trade and human trafficking. According to the 2011 Norton Cybercrime Report released by Symantec, 96 percent of the world’s Internet users have been victimized by cybercriminals at some point in their lives. Rapidly escalating cybercrime is one of the most pressing global challengers shared by both the Global North (GN) and Global South (GS). Nowadays cybercrimes are associated with the growing incidents of financial loss, intellectual property theft, breach of privacy as well as other social problems [2].
Speaking about cybercrimes particularly in the context of Latin America, it is important to emphasize that one of the basic preconditions for the proliferation of informational insecurity was the Internet’s rapid diffusion and digitalization of economic activities. Equally important are the forces of rapid globalization, which have led to a high degree of freedom in the movements of goods, services, capital, technology, and people, which have affected cybercrimes originating from and affecting as well as cybersecurity situations in the Global South. For example, there are situations in Latin America when cybercriminals travel to locations that are safe and where they face lower probability of arrests and conviction [2]. A reason why non-state criminal actors such as drug traffickers, money launderers and black market arms dealers are increasingly on the winning side is their sophistication and technological savviness. While the states hold some trump cards at the most basic level, many governments, especially, in the GS, lack technological sophistication and are poorly equipped to fight non-state criminal actors.
More than that, business and consumers in Latin America very often use technologies that a crime prone (ICT, cellphones, and cloud services) whereas local economies have not placed the appropriate level of effort on implementing systems to protect networks and information. One more reason why technologies used in economies in the GS are crime prone that they are outdated [2]. Some individuals engaged in cybercrime in the CS perceive themselves to be exploited by the GN and believe that it is morally more acceptable to victimize business and consumers in the GN than those in the CS.
To prove abovementioned theoretical points, I would like to pay attention to a concrete example of the country — Brazil — which plays a significant role in issues of cybersecurity. Brazil’s social, economic, political, and cultural characteristics provide unique and fascinating insights into the key drivers of cybercrimes and the nature of CS measures. The country is both a major source and a target of cyber-attacks. Some of the world’s well-known cybercriminal gangs operate from the country.
Brazil has earned its reputation as the “king of the banking Trojan”. Whereas cybercriminals mostly rely on a small number of malware products in most other parts of the world, the Brazilian malware landscape is more diverse. In 2004, losses from online financial fraud in Brazil were estimated to exceed losses through bank robberies [3].
In addition, Brazil is also exposed to politically-motivated internal cyber-threats. In 2008, hackers attacked a government website and compromised valuable documents. The hacker demanded US$350 million in ransom money. The ransom was not paid but it took more than a week to regain control of the website [3].
Brazil is also reported to be among the top countries in terms of the government’s actions to control and monitor citizens’ activities online. For instance, Google has reported that Brazil is among the countries making highest numbers of requests to obtain user information or to block search results through legal actions. According to Brazil’s speech laws, public officials have the power and authority to decide what is considered as libel, slander or defamation of character [3].
Nevertheless, IP theft and industrial espionage are not currently a major concern in Brazil. However, the country is exposed to significant cyber-threats thanks to the country’s financially and politically motivated cybercriminal gangs. Equally problematic has been the lack of spending on core CS assets. One more characteristic of Brazilian cybercrime landscape is that most cyber-attacks are domestically originated, which would make threat detection a difficult exercise. Besides, a large proportion of Brazilian computer users do not take remedial actions such as patching the systems. A difficulty is also a widespread use of unlicensed versions of Windows, which don’t have access to security updates [4].
As everybody knows, an appropriate infrastructure enhancement promotes growth, equity, and environmental sustainability. Infrastructure expansion in LAC region is unavoidable and essential to underpin future economic growth. In pursuing this goal, critical infrastructures (infrastructures of significant national importance) play a significant role. Modern societies rely heavily on critical infrastructures, such as electricity, gas, financial institutions, and information technology (IT) to perform day-to-day activities and implement future growth strategies [4].
There are two major trends that have considerable impact on CIIP approaches in LAC: urbanization and digitalization of infrastructures. First of all, the high concentration of the population in urban centers implies greater reliance on critical infrastructures and more significant implications of disruptions. The second trend is related to technological modernization of economic infrastructures. Today nearly all new infrastructure investments incorporate a “smart” component as part of the project. Thus, these trends create risks related to cyber threats to which all IT systems and networks are susceptible [5].
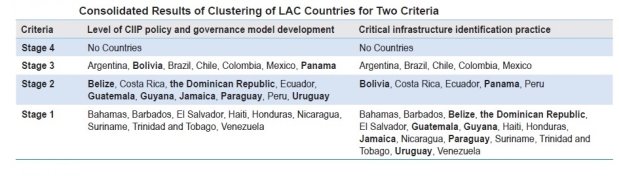
For better understanding of the problem, I would like to demonstrate the data from research made by Antonio García Zaballos. In his study, scientist clustered LAC countries into four groups based on two criteria: (1) level of development of CIP (critical infrastructure protection) policy and governance and (2) level of critical infrastructure identification and protection. The first criterion examined the level of CIP policy and governance model development. The second criterion reflects implementation of an existing CIP framework. In addition, the authors defined four stages of countries’ accordance to their criterion from most to less advanced [6].
In general, the LAC countries included in Stage 1 have a poor basis for CIIP. These countries have no practical approach in place to address CIIP, have made no progress in initiatives to secure and strengthen national critical infrastructures, and have not formally defined critical infrastructures. Countries clustered in Stage 2 understand the importance of CIIP and have addressed CIIP issues in one way or another. However, attempts are mostly fragmented, distributed between ministries, and there is no systematic approach at the national level or it is not fully implemented. Stage 3 encompasses LAC countries that stand out from the others because of the maturity of CIIP work performed. Although these countries have resources and practices in CIIP, there remain important gaps within their CIP frameworks and implementation efforts. This is why, no LAC countries were classified as Stage 4, which represents best practice countries that were analyzed within the context of this study [5].
As we can see in the table, none of the LAC countries has a perfect protection of its critical informational infrastructure, and in the long term, this problem may outgrow in a threat to the whole western hemisphere. In in my opinion, LAC countries should try to apply the tactics and knowledge of nations that have already achieved prominent results in this area.
Finland’s CIIP policy is a part of its national security framework. The main objectives of the framework are to secure functioning of the society, analyze risks, commission a governance model for emergency situations, and put in place responsibilities for all the actors, including private sector and nongovernmental organizations. The Government of Finland exemplified strong political leadership and responsibility for providing strategic guidelines and making the required decisions regarding allocating resources and prerequisites for CIIP.
The major advancements in CIIP framework development in Spain were made in 2007 with the approval of the very first National Plan for Critical Infrastructure Protection and National Catalogue of Strategic Infrastructure. Also in 2007, the government approved an agreement on Critical Infrastructure Protection authorizing the governance framework to direct and coordinate the necessary actions to protect critical infrastructures. In 2011, Spain adopted legislation that set the overall governance framework for CIIP, designating critical infrastructure sectors and various protection measures.
Korea began its digitalization campaign in the 1980s and, as a result, understood the need to protect digital records, privacy online, and the criticality of information infrastructure earlier than other countries. In 2004, Korea adopted the Act on the Management of Disasters and Safety, which installed a disaster and safety control system against various disasters to ensure citizen security, physical safety, and safety of property. The country is under constant cyber-attacks. Consequently, the government escalated cyberspace as another operational domain like the nation’s territories on land, air, and sea that need a state-level defense system.
Strengthening the security and resilience of critical infrastructures against both physical and cyber threats is one of the core policy objectives of the United States. At the strategic level, protecting critical infrastructures and key assets is among the core mission areas within the President’s National Strategy for Homeland Security. The current National Infrastructure Protection Plan (NIPP) provides guidance on efforts of stakeholders to enhance the security and resilience of critical infrastructures across the country in conjunction with national preparedness policy and integrates existing and future critical infrastructure security and resilience efforts into a single national program [6].
I strongly believe that this priceless experience can and has to be applied in the LAC region to strengthen local informational security capabilities, especially in the sphere of CIIP. In my opinion, the next list of the recommendations LAC countries may find useful to implement. Prioritization of CIIP at the national level: a significant level of engagement in implementing a CIIP framework can be achieved by prioritizing the CIP agenda at the national level and by developing primary national strategies. Overarching framework for CIIP: CIIP policies and legal frameworks benefit from a single overarching policy document that encompasses all related areas and actions and establishes the governance framework. Dedicate a CIIP body: operation and maintenance of CIIP requires dedicated attention and human and financial resources. Government should create an inter-agency body responsible for ensuring the resilience and protection of critical infrastructure from security threats. The CIIP body should be responsible for policy oversight of national infrastructure in collaboration with industry, develop mechanisms to improve information sharing between the interconnected sectors, investigate vulnerabilities at critical infrastructures, and perform security audits.
Assess risk: the aim of the exercise is to understand what risks are most likely to hinder national security, including economic security and citizen well-being. Database of identified critical infrastructure assets: information about all identified critical infrastructure assets should be stored in a centralized list. It is important to ensure that the national critical infrastructure list includes information about all critical infrastructure of national significance.
Partner with the private sector: it takes time and effort to build the level of trust and cooperation needed for CIIP. The public sector will need time to make an effort to be perceived as a strong partner in CIIP. Leveraging the national and regional academia for targeted CIIP research may be a good way to increase the capacity of the public sector in CIIP decision making and allow it to provide expertise and advice to the private sector. Skilled specialists and engineers: advanced skills are an important element of any CIP program. To effectively implement a CIP framework, the public and private sectors need skilled specialists. Countries need to invest in training and building the capacity of existing critical infrastructure personnel.
Information sharing: good information sharing requires a continuous effort to maintain strong relationships with information sharing partners. Manage security incidents: security incidents should be reported, investigated, and reacted to in a timely manner through efficient Security Incidents Management [6].
Nevertheless, it is not enough only to define the theoretical strategies and approaches for overcoming the problem of cybersecurity in LAC because now many countries in the region are preoccupied with more important problems, such as social needs, criminals, and drug trafficking. There is no doubt, the realization of beforementioned recommendations in some cases may demand the help from the outside. I think that the USA on the rights of “older brother” can provide Latin American countries with necessary support.
The U. S. has a real opportunity to lead in the hemisphere. Many governments in the region are working hard to develop or enhance their national cybersecurity frameworks and policies, and the U. S. is strongly positioned to help provide legal, policy and technical support to complement their efforts. This is the starting point for creating a more robust framework for international cooperation and common standards. More than that, Latin American countries encourage the USA to deepen cyber policy engagement in the region, and promote the need for balanced privacy regimes, cross border data flows, and the information-sharing mechanisms that are so critical to preventing, detecting and responding to cyber threats.
References:
- Brayman M. Tackling Cyber Criminals / M. Brayman. — Free Online Library. Business Mexico, 2016.
- Buscaglia C. How «Cybersafe» Are the BRICs? / C. Buscaglia. — Journal of Legal, Ethical and Regulatory Issues, 2012. — URL: https://www.questia.com/library/journal/1P3–2751576431/how-cybersafe-are-the-brics (date of access: 20.08.18)
- Fraser. J. Promote Americas-wide Collaboration on Cybersecurity / J. Fraser //Americas Quarterly. — URL: https://www.americasquarterly.org/content/promote-americas-wide-collaboration-cybersecurity (date of access: 20.08.18)
- Kshetri N. Cybercrime and Cybersecurity in the Global South / N. Kshetri. — Palgrave Mackmillan, 2013. — 261 p.
- Kshetri N. Cybersecurity in Brazil / N. Kshetri // The Quest to Cyber Security. — Springer, 2016. 195–209 p.
- Zaballos A. Best Practices for Critical Information Infrastructure Protection / A. Zaballos. — Inter-American Development Bank, 2016.